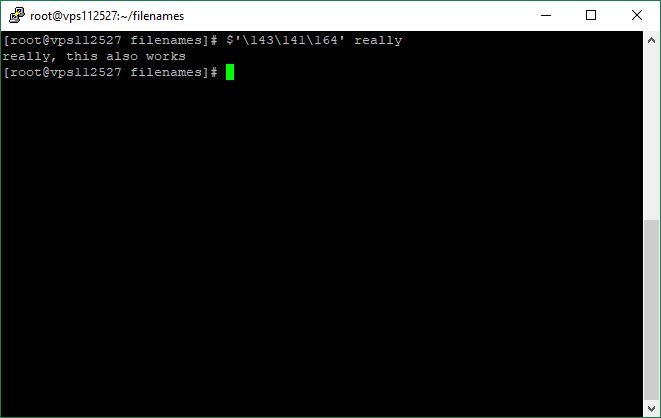
#linux #bash #obfuscation using octal vals
$'\143\141\164' really
gnu.org/software/bash/…
"Words of the form $'string' are treated specially. The word expands to string, with backslash-escaped characters replaced as specified by the ANSI C standard."

$'\143\141\164' really
gnu.org/software/bash/…
"Words of the form $'string' are treated specially. The word expands to string, with backslash-escaped characters replaced as specified by the ANSI C standard."
https://twitter.com/DissectMalware/status/1020794867952365568
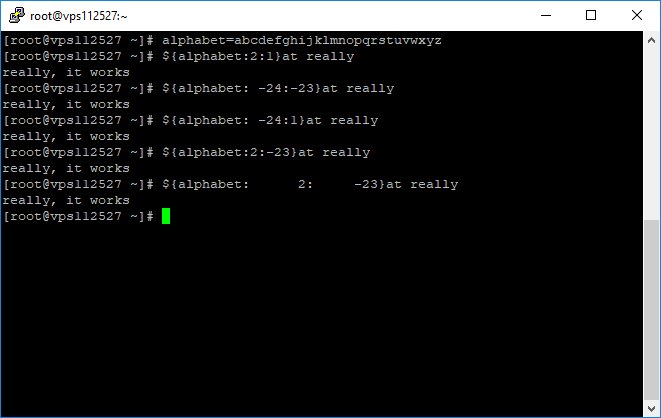
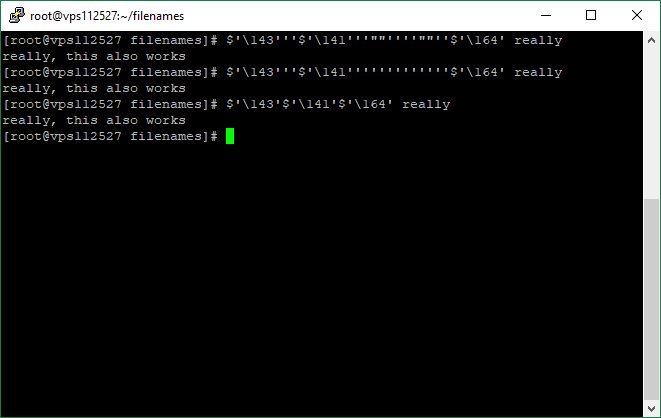
Variations
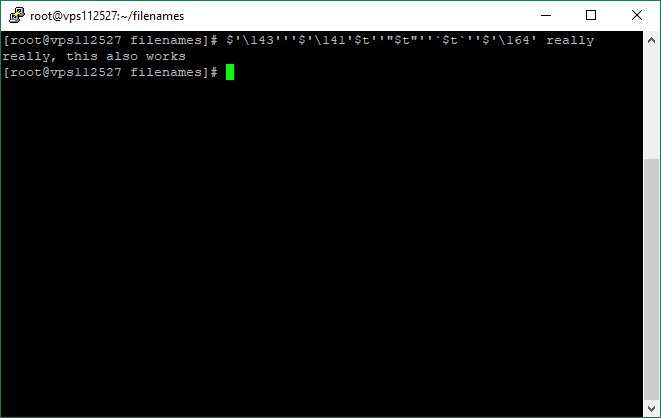
$'\143'$'\141'$'\164' really
$'\143'''$'\141'''''''''''''$'\164' really
$'\143'''$'\141'''""''''""''$'\164' really
Explanation:
'' -> empty string
""-> empty string
'a''b' -> 'ab' (concatenation)
(deleted the previous one, as the picture had a problem)
$'\143'$'\141'$'\164' really
$'\143'''$'\141'''''''''''''$'\164' really
$'\143'''$'\141'''""''''""''$'\164' really
Explanation:
'' -> empty string
""-> empty string
'a''b' -> 'ab' (concatenation)
(deleted the previous one, as the picture had a problem)
#bash #linux
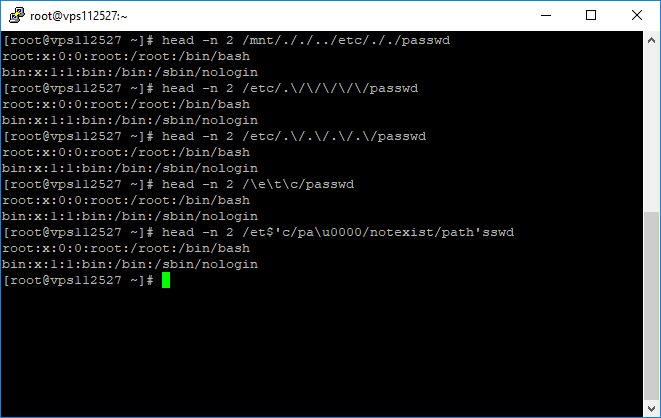
Using null character as filler for command #obfuscation
#empty strings
$'\x0'
$'\x00'
$'\x'
$'\000'
$'\00'
$'\0'
$'\u0000'
$'\u000'
$'\u00'
$'\u0'
$'\u'
$'\u0000000000000000'
$'\x000000000000'
$'\00000000000000000000'
Using null character as filler for command #obfuscation
#empty strings
$'\x0'
$'\x00'
$'\x'
$'\000'
$'\00'
$'\0'
$'\u0000'
$'\u000'
$'\u00'
$'\u0'
$'\u'
$'\u0000000000000000'
$'\x000000000000'
$'\00000000000000000000'
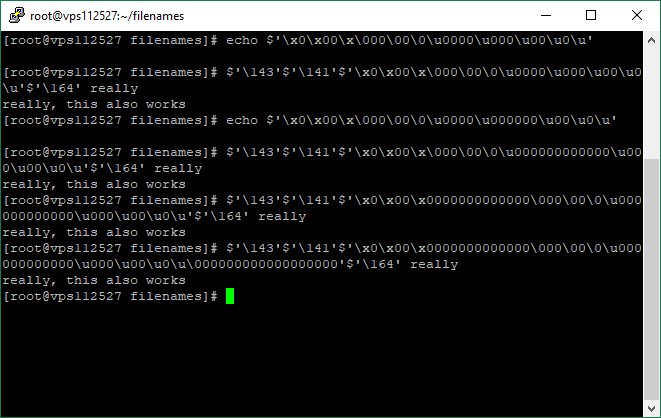
bonus?
#empty string
$'\u0000 anything you want enter here it will be ignored'
Explanation
\u0000 is a #null character, in bash end of string is a null character like c; thus anything after null is ignored
#empty string
$'\u0000 anything you want enter here it will be ignored'
Explanation
\u0000 is a #null character, in bash end of string is a null character like c; thus anything after null is ignored

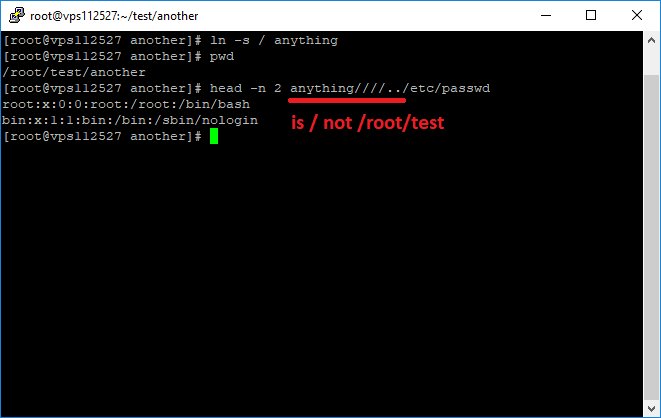
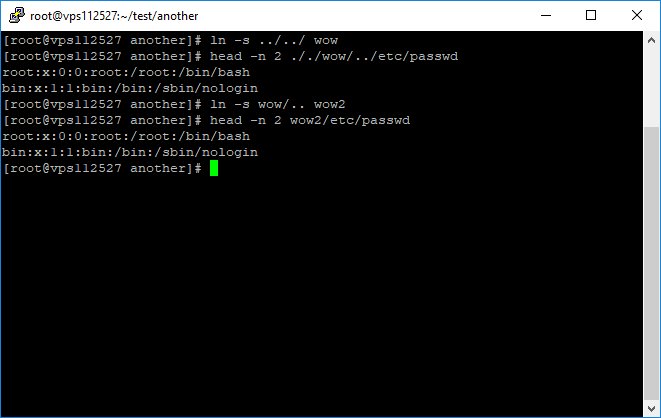
$'\143\141\164' is equivalent to 'cat'
really is a file
so basically we want to obfuscate the following command
cat really
really is a file
so basically we want to obfuscate the following command
cat really
* Correction
$'\u' and $'\x' are not #empty strings.
$'\u' and $'\x' are not #empty strings.
the picture is a little bit misleading, see the bonus to find out why.
For completeness
$'\U00000063\U0000061\U00074' really
"\UHHHHHHHH
the Unicode (ISO/IEC 10646) character whose value is the hexadecimal value HHHHHHHH (one to eight hex digits) "
$'\U00000063\U0000061\U00074' really
"\UHHHHHHHH
the Unicode (ISO/IEC 10646) character whose value is the hexadecimal value HHHHHHHH (one to eight hex digits) "
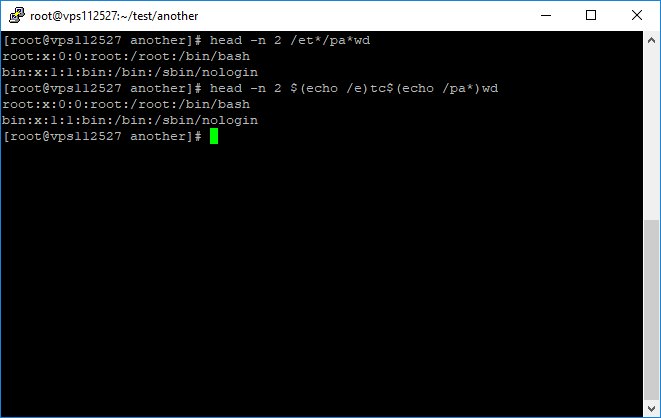
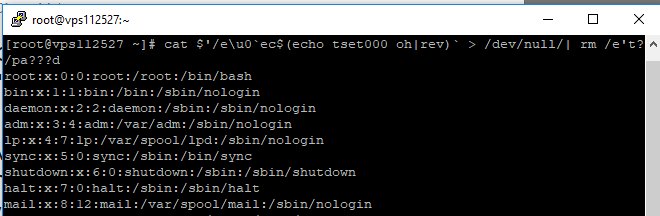
Want to test yourself:
what this command do?
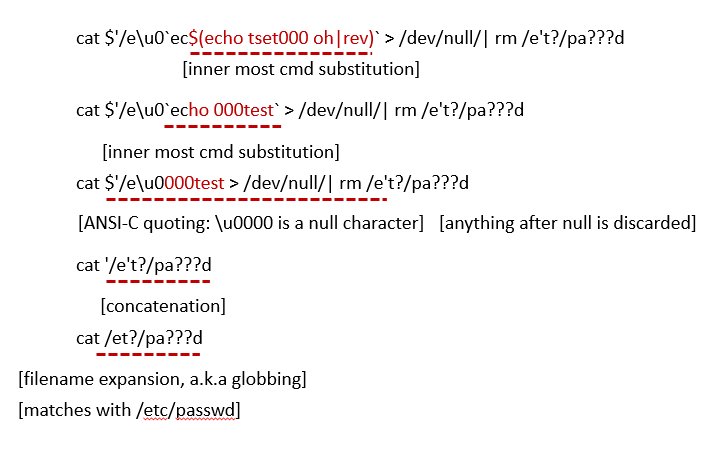
cat $'/e\u0`ec$(echo tset000 oh|rev)` > /dev/null/| rm /e't?/pa???d
(answer will be in the reply)
what this command do?
cat $'/e\u0`ec$(echo tset000 oh|rev)` > /dev/null/| rm /e't?/pa???d
(answer will be in the reply)
#bash #deobfuscation of the previous tweet
[1] $(echo tset000 oh|rev) # ho 000test
[2] `ec[1]` -> `echo 000test` # 000test
[3] $'/e\u0[2] > /dev/null/| rm /e' # '/e\u0000' after null will be truncated
[4] cat [3]t?/pa???d # cat /et?/pa???d
[5] cat /etc/passwd
[1] $(echo tset000 oh|rev) # ho 000test
[2] `ec[1]` -> `echo 000test` # 000test
[3] $'/e\u0[2] > /dev/null/| rm /e' # '/e\u0000' after null will be truncated
[4] cat [3]t?/pa???d # cat /et?/pa???d
[5] cat /etc/passwd
• • •
Missing some Tweet in this thread? You can try to
force a refresh