#linux #bash #path #obfuscation
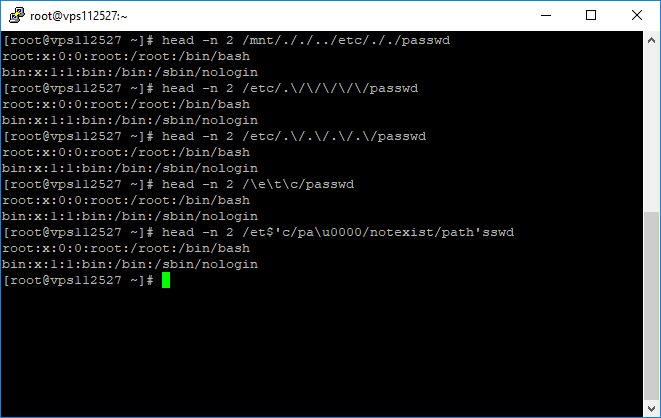
goal: obfuscate /etc/passwd
1) #directorytraversal: /mnt/././../etc/././passwd
2) escape characher: /etc/.\/\/\/\/\/passwd /etc/.\/.\/.\/.\/passwd /\e\t\c/passwd
3) null character /et$'c/pa\u0000/notexist/path'sswd
....
goal: obfuscate /etc/passwd
1) #directorytraversal: /mnt/././../etc/././passwd
2) escape characher: /etc/.\/\/\/\/\/passwd /etc/.\/.\/.\/.\/passwd /\e\t\c/passwd
3) null character /et$'c/pa\u0000/notexist/path'sswd
....
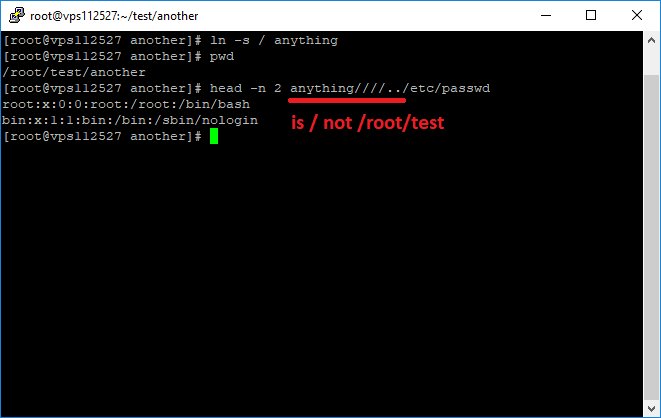
#path #obfuscation using #symbolic #link
ln -s / anything
head -n 2 anything////../etc/passwd
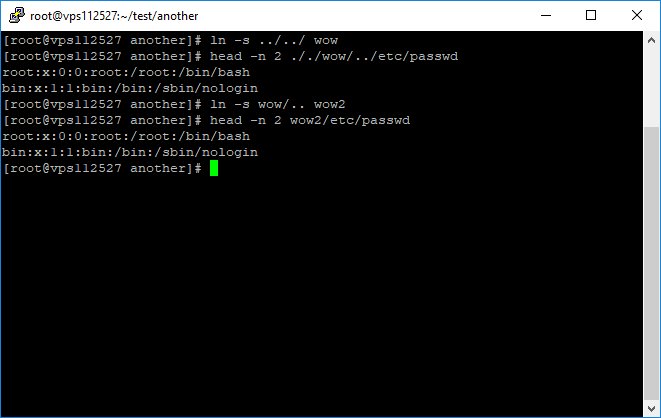
ln -s ../../ wow
head -n 2 ././wow/../etc/passwd
* ../ after a sym link applies to the sym link not the current path

ln -s / anything
head -n 2 anything////../etc/passwd
ln -s ../../ wow
head -n 2 ././wow/../etc/passwd
* ../ after a sym link applies to the sym link not the current path
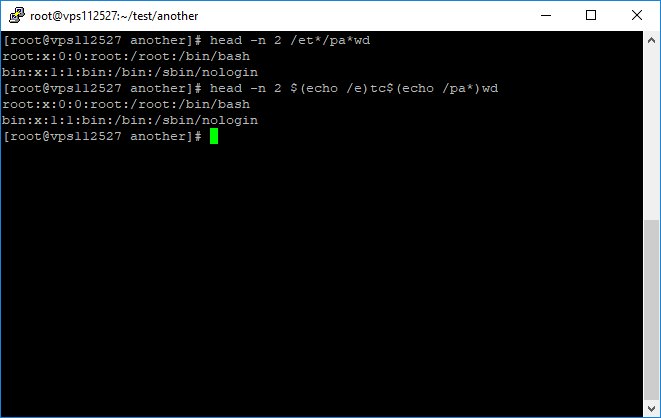
filename expansion #globbing
cat /et*/pa**wd
command expansion
$(echo /e)tc$(echo /pa*)wd
+ other string obfuscation techniques
cat /et*/pa**wd
command expansion
$(echo /e)tc$(echo /pa*)wd
+ other string obfuscation techniques
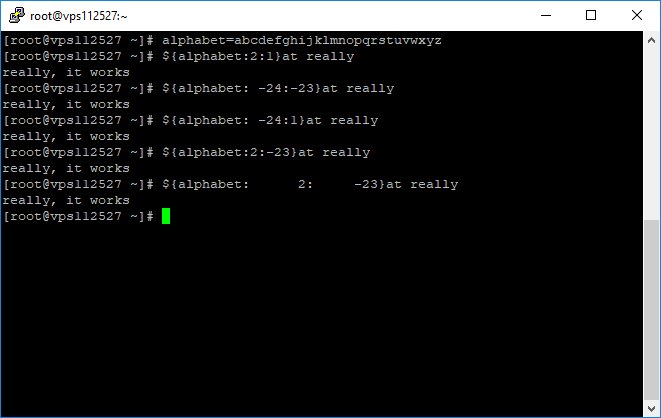
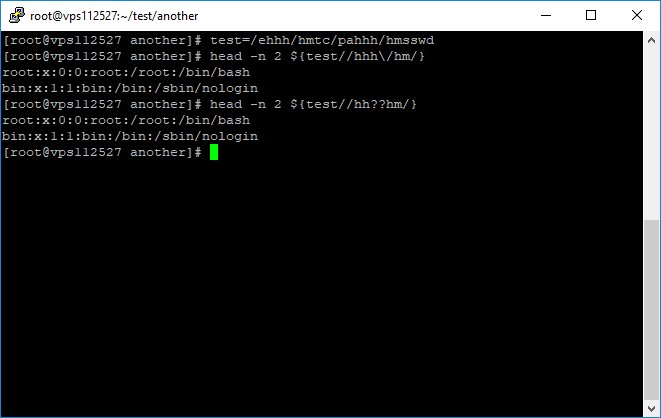
#bash #obfuscation by string manipulation
${var//pattern/string} --> Find and replace all occurrences of pattern in var by string
test=/ehhh/hmtc/pahhh/hmsswd
${test//hhh\/hm/}
${test//hh??hm/}
are equal to /etc/passwd
${var//pattern/string} --> Find and replace all occurrences of pattern in var by string
test=/ehhh/hmtc/pahhh/hmsswd
${test//hhh\/hm/}
${test//hh??hm/}
are equal to /etc/passwd
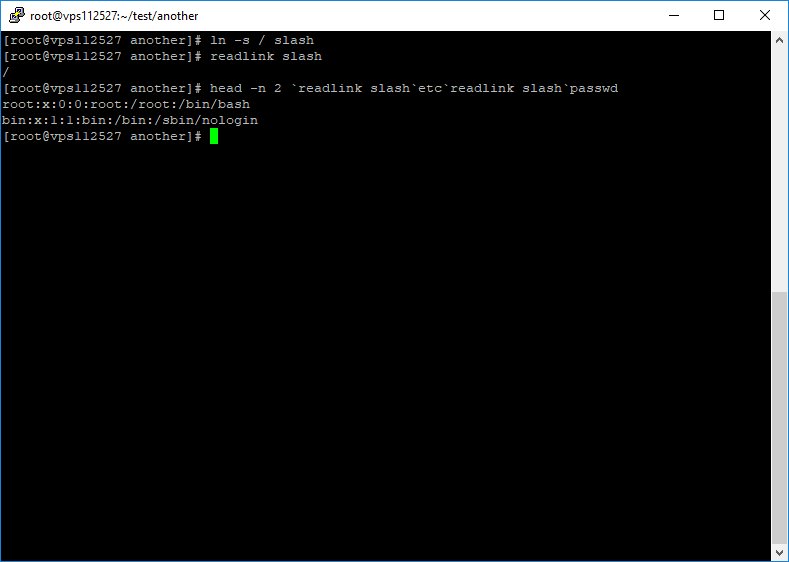
Using #symbolic #link (#softlink) for #path #obfuscation
You can read the file path referred to by a soft link with #readlink command.
Note: soft link is a special file that its content is supposed to be a path. But one can store anything there!
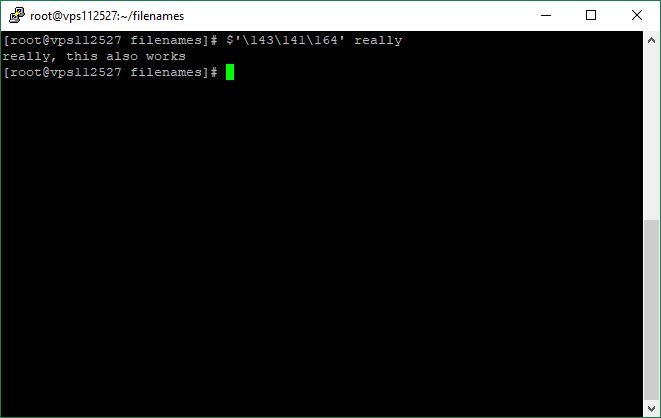
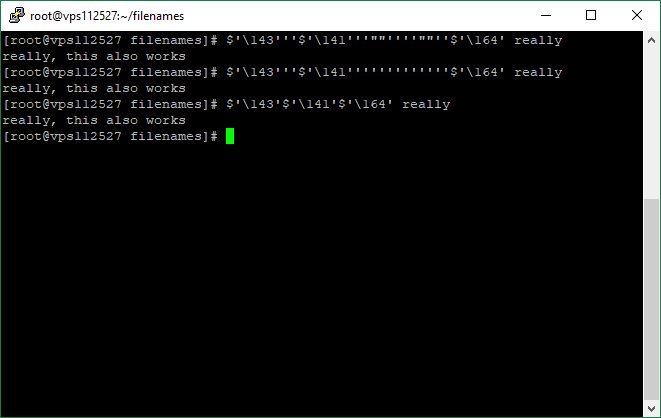
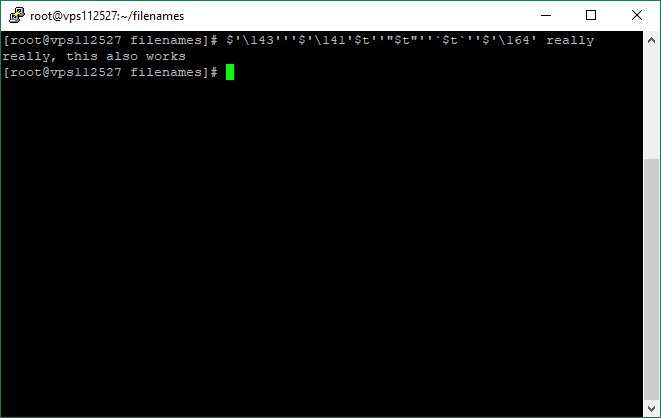
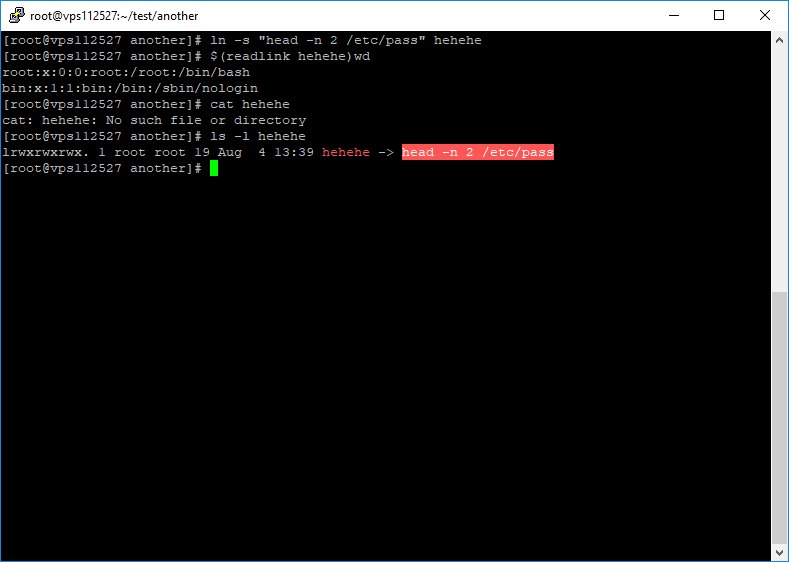
#command #obfuscation #bash

You can read the file path referred to by a soft link with #readlink command.
Note: soft link is a special file that its content is supposed to be a path. But one can store anything there!
#command #obfuscation #bash
• • •
Missing some Tweet in this thread? You can try to
force a refresh