Exploring the emergence & evolution of the #Bitcoin #business #ecosystem. The following network graphs are based on dataset of 514 entities.
Bitcoin business ecosystem - 2010 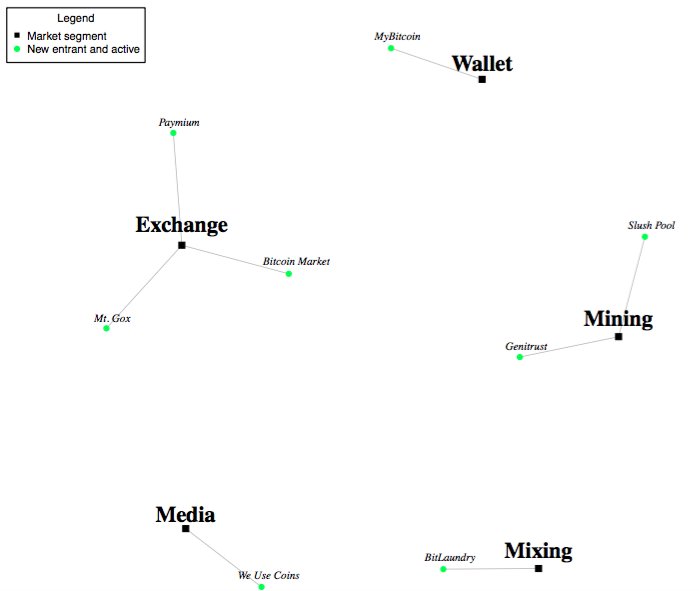
• • •
Missing some Tweet in this thread? You can try to
force a refresh