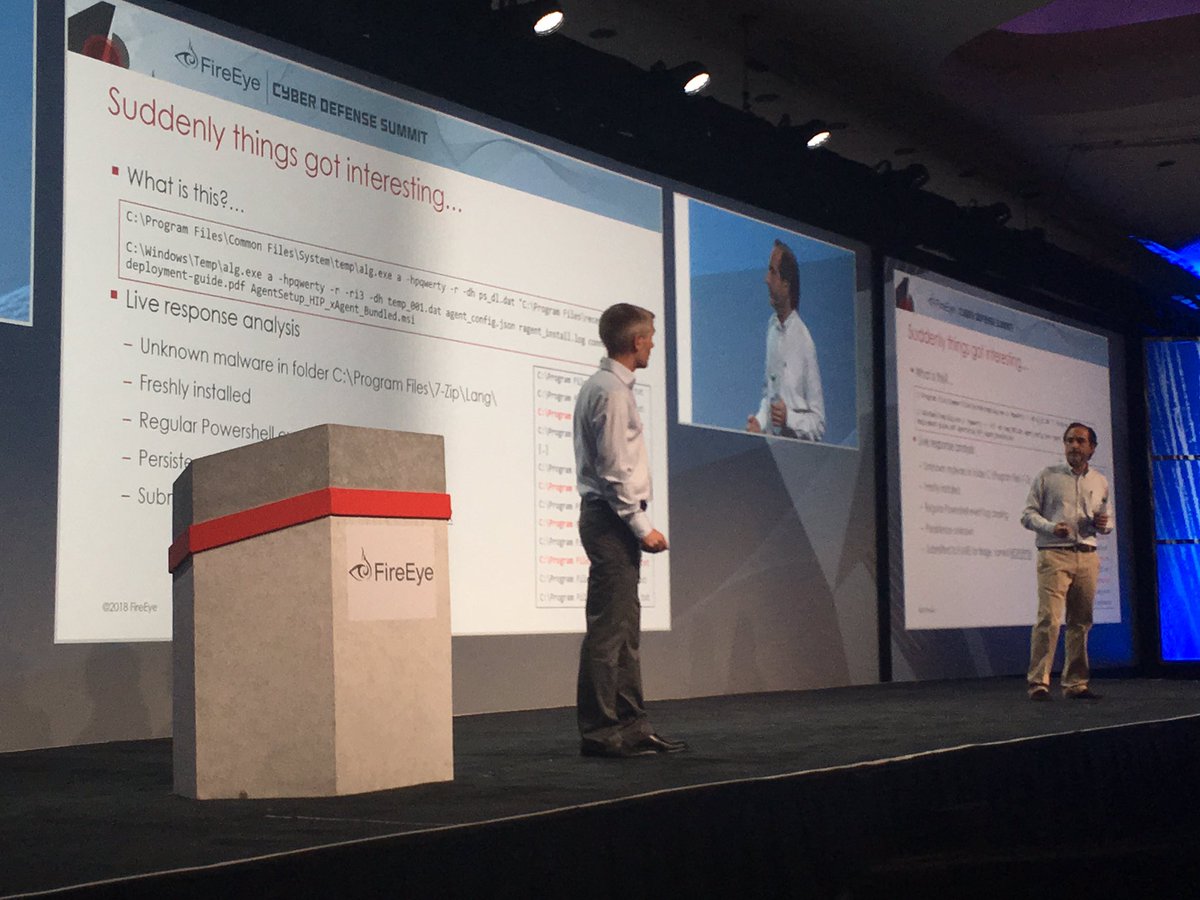
First up Matias and Adrian discussing investigating the threat actor that MSFT calls Platinum
...and right out of the gate the threat actor steals your EDR agent installer 😮 #SignsThisProbablyIsntAScriptKiddie
#FireEyeSummit
...and right out of the gate the threat actor steals your EDR agent installer 😮 #SignsThisProbablyIsntAScriptKiddie
#FireEyeSummit
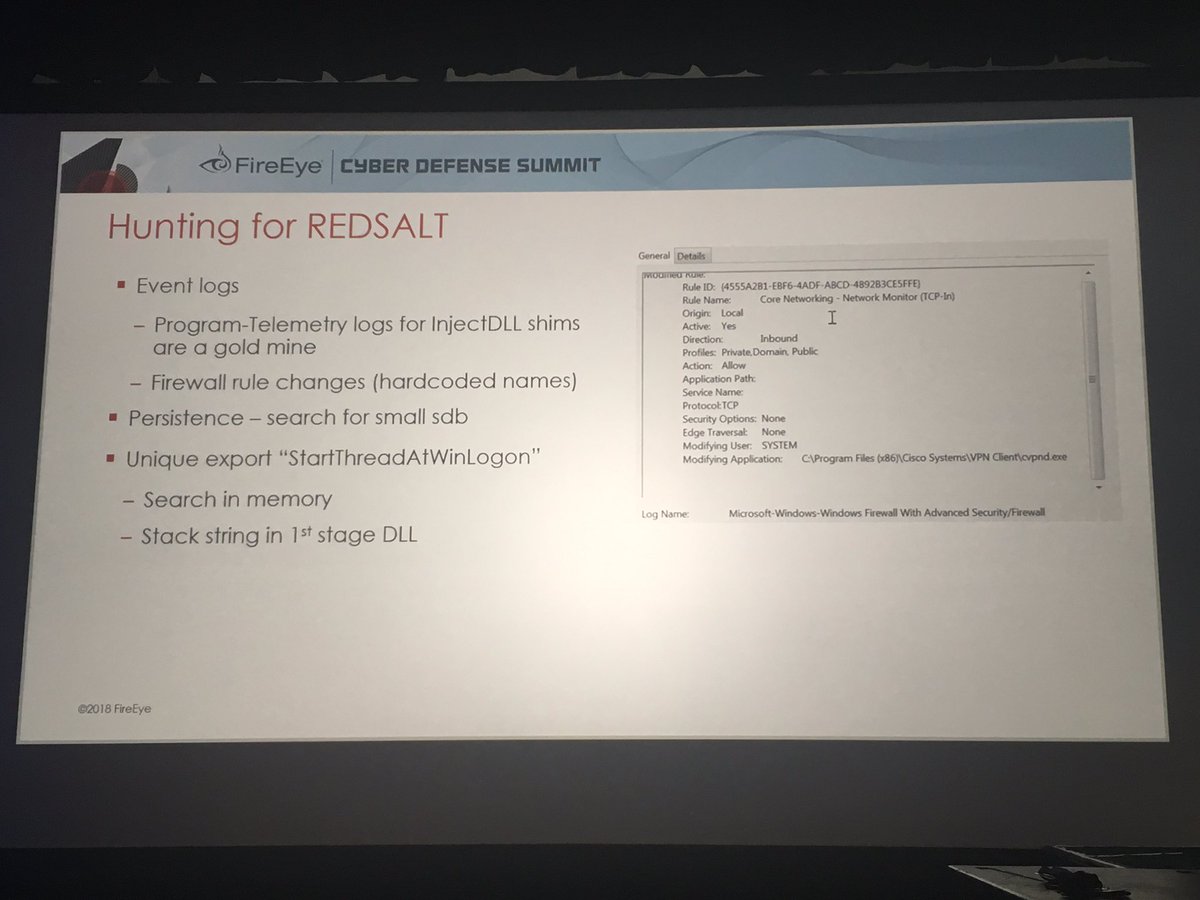
How do you hunt for ACI Shim persistence? Multiple different techniques - but the Windows Program-Telemetry logs are a great place to look
#FireEyeSummit
#FireEyeSummit
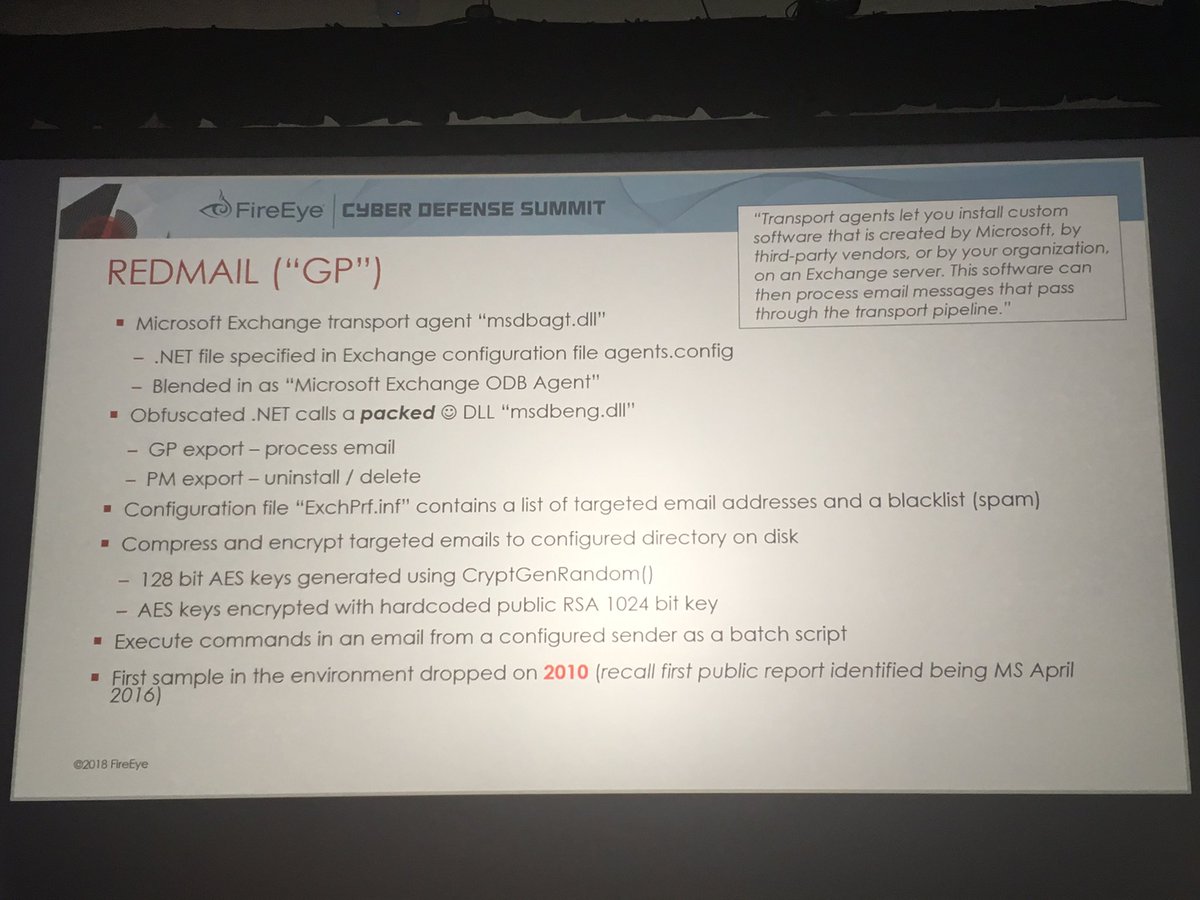
Ever heard of a Microsoft Exchange transport agent? Neither had I prior to this case
Actor monitored email for list of accounts & stored encrypted copy on disk
My favorite part is you can get remote command execution by emailing a specific account w/ a command
#FireEyeSummit
Actor monitored email for list of accounts & stored encrypted copy on disk
My favorite part is you can get remote command execution by emailing a specific account w/ a command
#FireEyeSummit
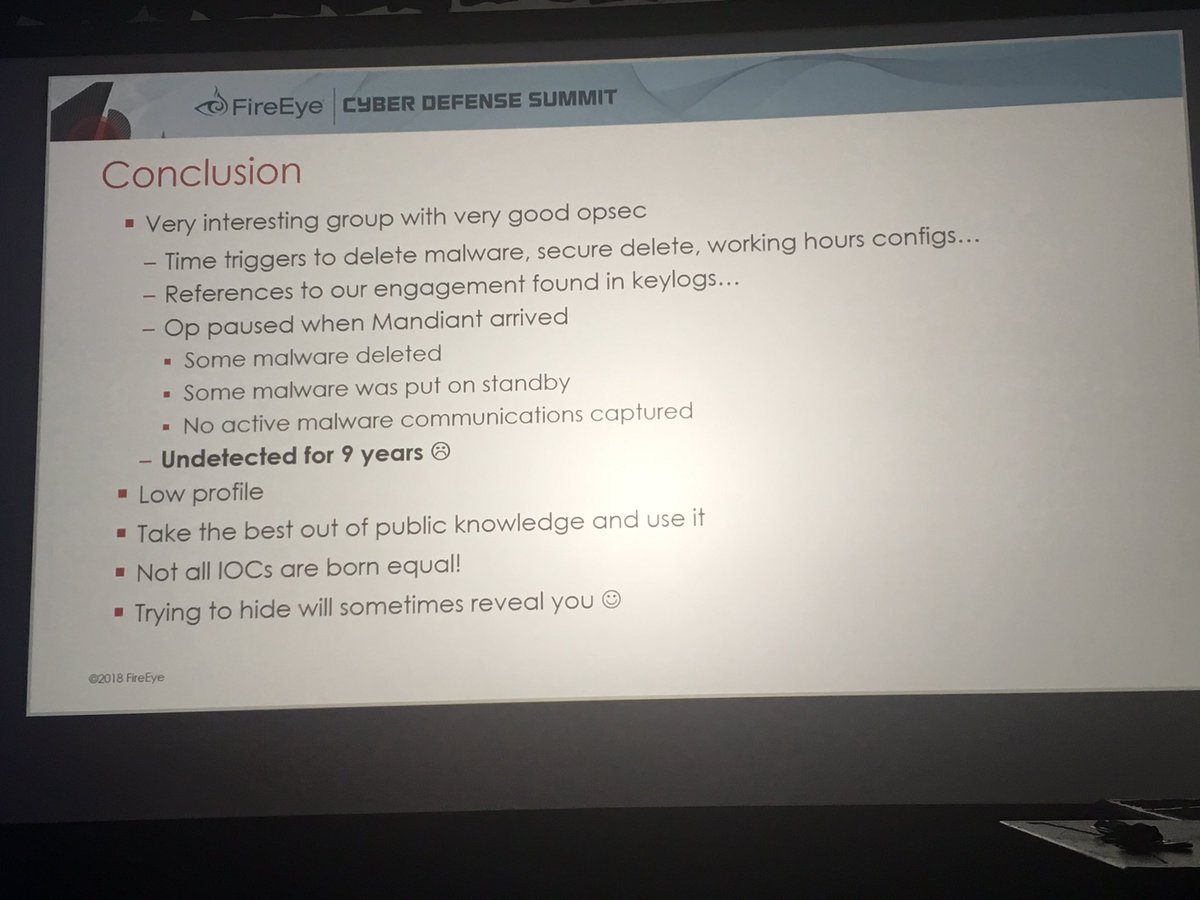
Unique things about "Platinum"
ACI Shim persistence
WMI persistence (back in 2010)
Port knocking
AMT Serial Over LAN for C2
Bootkits
Exchange transport agent
Undetected for 9 years
Actor learned @Mandiant was engaged & stopped ops 2 days prior to investigation
#FireEyeSummit
ACI Shim persistence
WMI persistence (back in 2010)
Port knocking
AMT Serial Over LAN for C2
Bootkits
Exchange transport agent
Undetected for 9 years
Actor learned @Mandiant was engaged & stopped ops 2 days prior to investigation
#FireEyeSummit
• • •
Missing some Tweet in this thread? You can try to
force a refresh